To all who whispered, reached, or wrote — I see your minds, I read your note,
Your sparks of thought still light the skies, you’re sharper than the keenest eyes.
Still standing strong, through night and flame, you brave the code, you play the game,
No hint too deep, no clue too small — we’ll crack this cipher, one and all.
Yet maybe now, to shift the flow, we twist the path, not straight, but slow,
A sideways step, a stranger hue — might show us signs we never knew.
So wash the grid, let numbers spin — a bigger matrix hides within,
Let logic swirl, let order bend — the deeper wash might mark the end.
The clock runs fast, no time to wait, the prize awaits, so tempt your fate,
The one who strikes the code’s last chord — shall claim the truth and take reward.
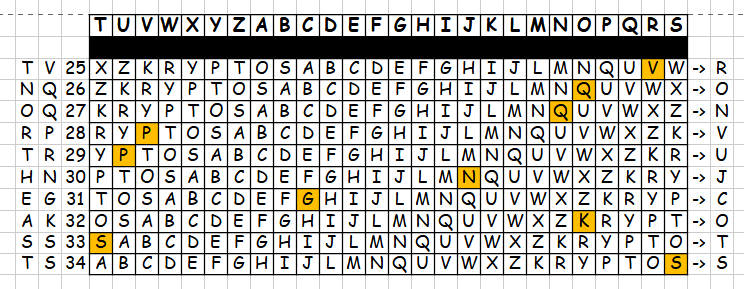
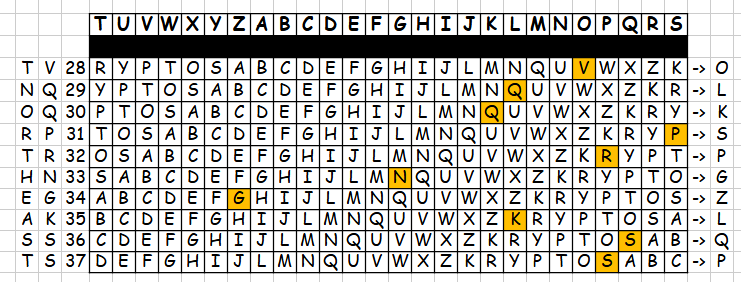
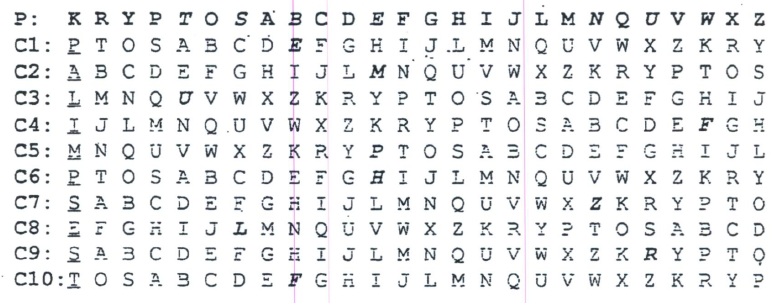
#3.1 – washing bigger matrix & EAS
- As some of you noticed, it is not working at all for first EAST (& BERLIN CLOCK).
- Lets check.
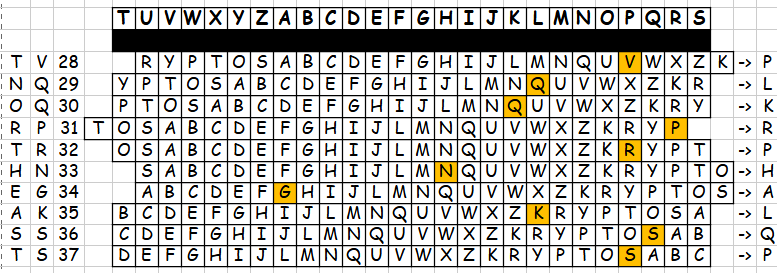
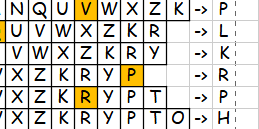
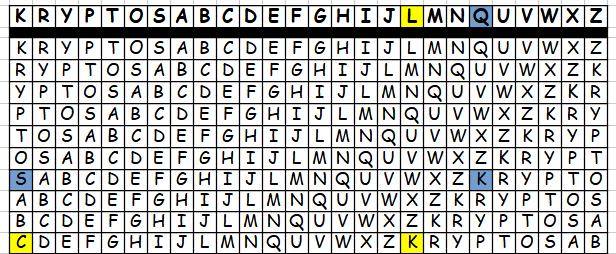
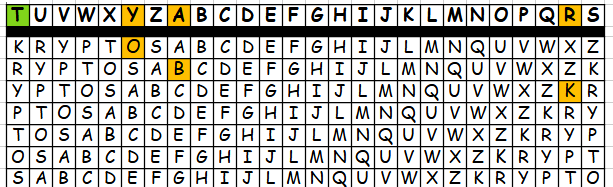
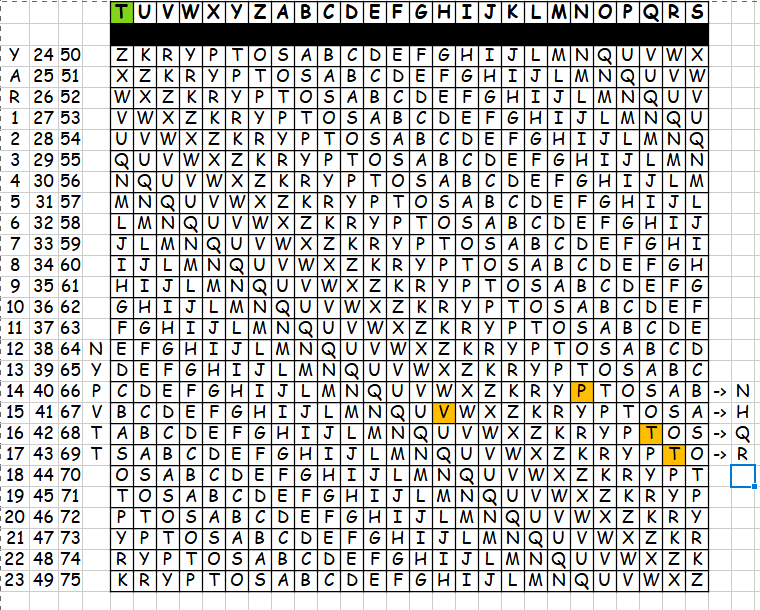
- We take our main matrix and rotate:
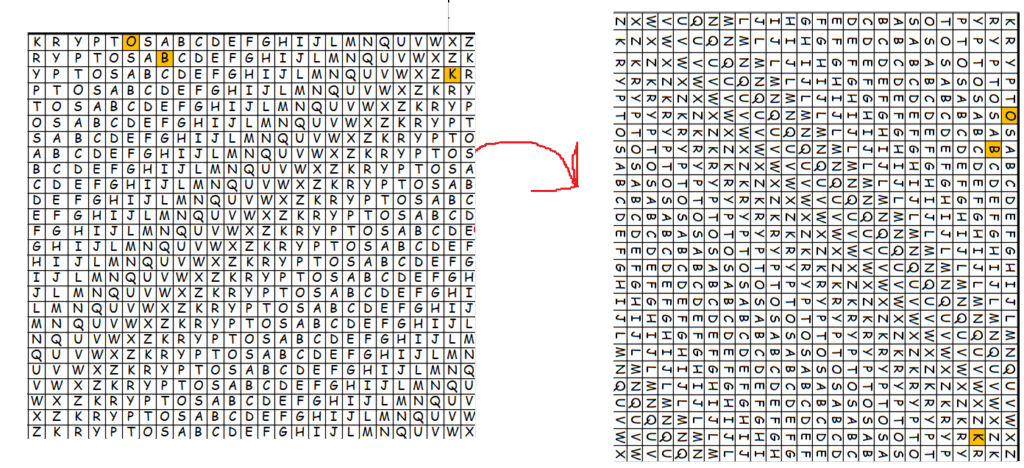
- If we again skip first 3 rows (used for YAR), then 22 letter falls into 25th row.:
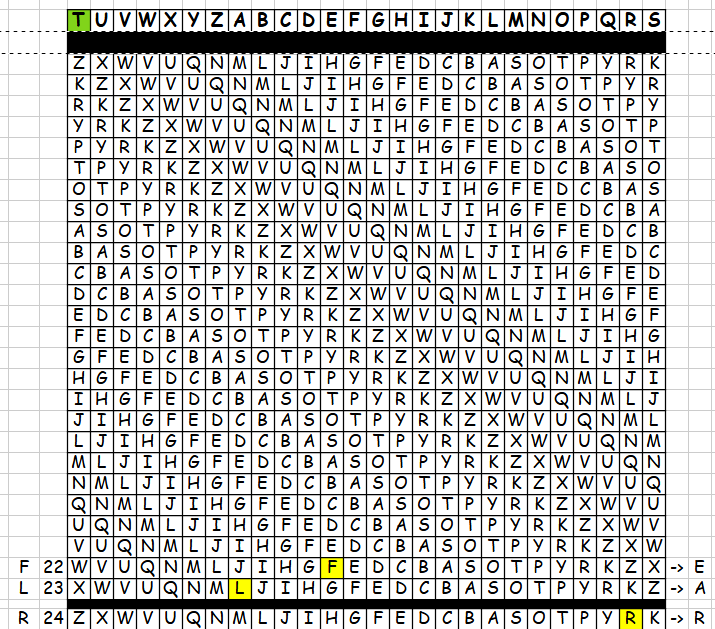
- Now we have: FLR → EAR, if we move Z row 1 position right, we end up having EAS
- the masking matrix (smaller) seems to be identity here?
- so should we rotate also bigger matrix?
#3.2 – washing both matrixes & (BE)RLIN
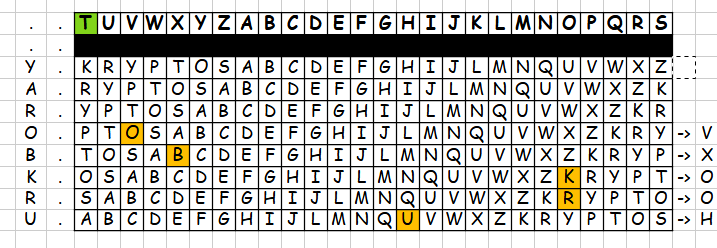
- Lets check with BERLIN:
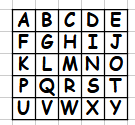
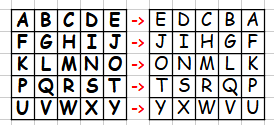
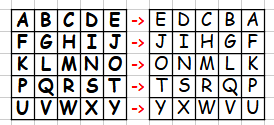
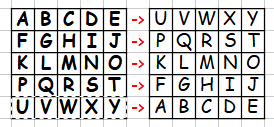
- smaller matrix: swap across A-Y diagonal
- masking for RLIN → NHQR
- bigger matrix: rotate left:
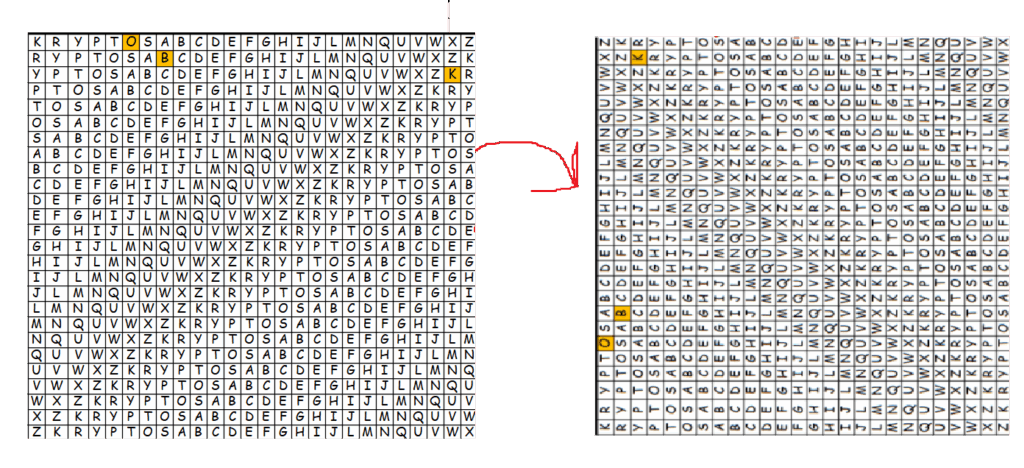
- again, skip first 3 rows, find where RLIN fits, reverse and … PVTT → NHQR, exactly what we had from masking with smaller matrix.
Eyes up high, seek what’s obscure,
The next reveal will shake the core.
No magic code, no hacker bluff,
I shaped a riddle, sharp and rough.
Kryptos related. English language. Pen and Paper.
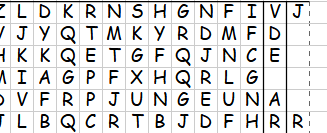
P4DC8 B3B9W BFMAS K3CFQ W51IF RMUTP XXFNB
AMUQL T9ZT5 FFRHU 1MLTR AS7M1 VD9WF LDNBT
CMQSX 22Q03 F3PU1 HQNXH TXJ3S 6534N LU15N
ZMRF1 QW515 PZUAY 2SL4F PHPP2 5WY5R H9814
PGLL5 V52B5 JHIH7 UH4Y5 6DX4B 5V54P XFOA2
653AC TSN5P HCTFP XID3A 1J669 92XQE PYS53
IRAUC IZ6M2 SALVF 2ECDF LNT6J G6FMI OC3U7
XRHLH U4J3M X3C5W LDX8J RM5IA HO3DG WXPU8
XHCTF PYVV3 4CP53 BJHUQ S8NR5 L8XUL 0Y0WY
FGWYI 5REC3 JW89O 7P59N RE2PM 7OBN9 7FMZN
0XINP K7MMX XVTXM P2MOC TCSJ5 CWO2E TP2EZ
0
Eyes up high, seek what’s obscure,
The next reveal will shake the core.